CISA added roughly 20 vulnerabilities to the Known Exploited Vulnerabilities catalog in April 2026. Five of them are critical enough to hand an attacker full control of your network infrastructure.
If you manage Fortinet, Cisco SD-WAN, or Windows servers running IPsec, stop reading after each CVE and check your patch status before continuing.

Here’s what to fix. Right now.
What Is CISA KEV and Why Does It Matter to Network Engineers?
The CISA KEV catalog is the U.S. Cybersecurity and Infrastructure Security Agency’s live list of CVEs confirmed to be actively exploited in the wild. Not theoretical. Not “could be used.” Actually being used, against real targets.
Every entry meets three criteria:
- Has an assigned CVE ID
- Has clear remediation guidance available
- Has reliable evidence of active exploitation in the wild
Under Binding Operational Directive 22-01 (BOD 22-01), all U.S. federal civilian agencies must patch KEV-listed vulnerabilities within set deadlines – usually 14-21 days, and as short as 3 days for the most urgent entries.
Private companies aren’t legally bound by BOD 22-01. But a CISA KEV listing means one thing: attackers are using this vulnerability right now. The government is telling you to patch it. The private-sector answer should be the same.
April 2026’s Patch Tuesday alone fixed 167 flaws. Total KEV additions for the month sat around 20 CVEs. These five rose to the top.

The 5 Most Critical CISA KEV Entries of April 2026
CVE #1: CVE-2026-21643 – Fortinet FortiClient EMS SQL Injection (CVSS 9.8)
Pre-authentication SQL injection. No credentials required. Actively exploited since 2026-03-31 as a zero-day.
What an attacker gets: A crafted request to the publicly accessible /api/v1/init_consts API endpoint extracts admin password hashes, API tokens, JWT secrets, and a complete inventory of every managed endpoint – hostnames, IP addresses, OS versions, serial numbers. The full picture of your endpoint fleet, handed over without a login.
This isn’t a “could lead to compromise” scenario. It’s direct database access from the internet.
Timeline:
| Event | Date |
|---|---|
| First exploited (zero-day) | 2026-03-31 |
| CISA KEV added | 2026-04-13 |
| FCEB patch deadline | 2026-04-27 |
Scale of exploitation: CrowdSec tracked 51 distinct attacking IP addresses against FortiClient EMS in a single week after disclosure. Arctic Wolf observed exploitation from the day the zero-day window opened. Approximately 2,000 internet-exposed instances remained unpatched as of late April.
What to do:
- Upgrade to FortiClient EMS 7.4.5 immediately
- If you can’t patch right away, remove the EMS management interface from internet exposure entirely
- Restrict API access to management network segments only
- Audit API access logs from 2026-03-31 forward for indicators of compromise
If you’re running Fortinet infrastructure and want to understand what the certification track actually teaches about designing secure management planes, our Fortinet NSE4 vs. Cisco Security comparison breaks down how each vendor’s training covers these architectural decisions.
CVE #2: CVE-2026-33824 – Windows IKE Service Extensions RCE (CVSS 9.8, Wormable)
Wormable remote code execution. No authentication. No user interaction. Every Windows host running IPsec or a Windows VPN endpoint is exposed.
What it is: A double-free memory corruption flaw in the Windows Internet Key Exchange service extensions (IKEEXT). An attacker sends crafted UDP packets to port 500 or port 4500 and achieves SYSTEM-level code execution. Once one host is compromised, it can automatically attack adjacent Windows servers. That’s what wormable means.
Who’s at risk: Windows 10, Windows 11, and all supported Windows Server versions with IPsec enabled. That covers most domain-joined corporate environments with site-to-site VPNs, any Windows server acting as a VPN endpoint, and every host with default domain IPsec policies applied by Group Policy.
Patched: 2026-04-14 (April Patch Tuesday). Microsoft rated this “Exploitation More Likely” – their way of saying: expect exploitation to follow disclosure quickly.
What to do:
- Apply the April 2026 Patch Tuesday cumulative update on all Windows systems now
- Temporary workaround: block inbound UDP 500 and 4500 on perimeter firewalls for systems that don’t require IKE. Restrict to known peer IP addresses via ACLs for those that do.
- Audit all Windows servers for active IPsec policies:
netsh ipsec static show allgives you the full picture - Check Group Policy for any domain-wide IPsec assignments that might leave unexpected hosts exposed
CVE #3: CVE-2025-32975 – Quest KACE SMA Authentication Bypass (CVSS 10.0)
CVSS 10.0. A perfect score. And the patch was available for 11 months before this hit the KEV catalog.
What it is: A complete authentication bypass in Quest KACE Systems Management Appliance. An attacker exploits a flaw in the SSO mechanism to impersonate any legitimate user – including administrators. No credentials. No brute force. Just a malformed request the SSO logic accepts as valid.
What attackers do after getting in:
- Mimikatz-based credential extraction from managed endpoints
- Creation of rogue admin accounts that survive patching
- Lateral movement to RDP hosts, backup servers, and domain controllers
- Full visibility into the managed endpoint fleet, same as a legitimate KACE administrator
Timeline:
| Event | Date |
|---|---|
| Patch released by Quest | 2025-05 |
| First active exploitation | 2026-03-09 |
| CISA KEV added | 2026-04-20 |
| FCEB patch deadline | 2026-05-04 |
The uncomfortable reality: this vulnerability had a fix available for 11 months. It only entered active exploitation because organisations didn’t apply it. This is a textbook preventable breach.
What to do:
- Apply the KACE SMA patch from May 2025 if you haven’t already
- Audit KACE admin logs from 2026-03-09 forward for any account creation events or unusual API calls
- Review all admin accounts and remove any that weren’t explicitly created by your team
- Check your asset inventory for any KACE instances that may have been deployed and forgotten
CVE #4: Cisco Catalyst SD-WAN Manager – Triple Vulnerability Chain

Three separate CVEs in one product. One coordinated attack chain. Your entire SD-WAN deployment at risk.
The three CVEs:
| CVE | CVSS | Type | What It Gives an Attacker |
|---|---|---|---|
| CVE-2026-20133 | 6.5 | Unauthenticated info disclosure | Remote system enumeration without credentials |
| CVE-2026-20128 | 7.5 | Credentials in recoverable format | DCA credential extraction |
| CVE-2026-20122 | 5.4 | Improper privileged API usage | File upload and privilege escalation |
Why three medium-severity CVEs make this top-5 list: None of these alone is catastrophic. Chained together, they give an attacker full administrative control of your Cisco Catalyst SD-WAN Manager – the central controller for your entire SD-WAN deployment.
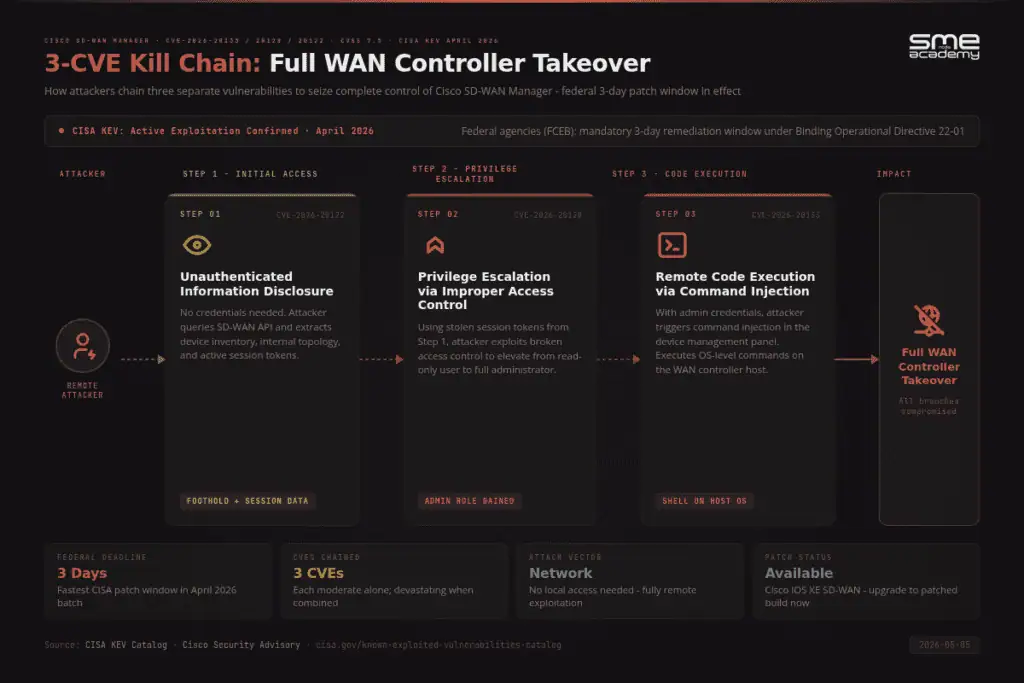
Compromise SD-WAN Manager and you can see every branch site, reroute traffic, intercept VPN tunnels, and pivot laterally across the WAN. This isn’t a single-site breach. It’s the keys to every location your SD-WAN connects.
Timeline:
| Event | Date |
|---|---|
| First exploitation observed | 2026-03 |
| CISA KEV added | 2026-04-20 |
| FCEB patch deadline | 2026-04-23 |
Three days. That’s the deadline CISA set for federal agencies. In the context of CISA KEV deadlines, that’s one of the shortest they issue. It signals that CISA viewed WAN infrastructure compromise as the highest-priority risk in April’s batch.
What to do:
- Apply patches for all three CVEs from Cisco’s security advisory portal
- Restrict SD-WAN Manager API access to management network segments only – it should never be internet-exposed
- Audit API access logs from March 2026 forward for any unusual authentication patterns or unexpected configuration changes
- Rotate DCA credentials immediately after patching
For engineers building towards formal Cisco security certification, our CCIE Security programme covers SD-WAN security architecture in depth – including proper management plane segmentation and access control design for SD-WAN Manager deployments.
CVE #5: CVE-2026-34621 – Adobe Acrobat Reader Prototype Pollution Zero-Day (CVSS 8.6)
A 5-month zero-day. Weaponised for geopolitical targeting before the vulnerability was even publicly known.
What it is: A prototype pollution vulnerability in Adobe Acrobat Reader’s JavaScript engine. A malicious PDF with obfuscated JavaScript modifies the application’s JavaScript prototype chain, bypassing security controls. The attack is two-stage: stage one fingerprints the system and exfiltrates data to a command-and-control server, and stage two launches further exploits based on what it finds.
Why network engineers specifically need to care: Your team receives PDFs constantly – vendor advisories, network diagrams, RFPs, compliance documentation. Every unpatched Acrobat Reader on every engineer’s workstation is a phishing entry point directly into your network.
Timeline:
| Event | Date |
|---|---|
| First exploitation observed | 2025-11 |
| Vulnerability publicly discovered | 2026-04 |
| CISA KEV added | 2026-04-13 |
| FCEB patch deadline | 2026-04-27 |
Malware samples recovered from this campaign contained Russian-language text referencing gas supply disruptions – indicating a state-linked threat actor used this as a targeted weapon for 5 months before anyone in the security community discovered it.
What to do:
- Update Acrobat DC to v26.001.21411 or later (Windows) / v24.001.30360 (macOS)
- Update Acrobat 2024 to v24.001.30362 (Windows) or v24.001.30360 (macOS)
- Enable automatic updates in Adobe’s built-in update manager
- For environments where PDF JavaScript isn’t needed: disable it. Go to Edit > Preferences > JavaScript > uncheck “Enable Acrobat JavaScript”. This removes the attack surface without affecting most legitimate PDF use cases.
April 2026 CISA KEV – Patch Priority at a Glance
| CVE | Product | CVSS | Auth Required | Attack Vector | FCEB Deadline |
|---|---|---|---|---|---|
| CVE-2025-32975 | Quest KACE SMA | 10.0 | None | Network | 2026-05-04 |
| CVE-2026-21643 | Fortinet FortiClient EMS 7.4.4 | 9.8 | None | Network | 2026-04-27 |
| CVE-2026-33824 | Windows IKE (IKEEXT) | 9.8 | None | Network (wormable) | 2026-04-28 |
| CVE-2026-34621 | Adobe Acrobat Reader | 8.6 | None | Local (PDF) | 2026-04-27 |
| CVE-2026-20133/28/22 | Cisco Catalyst SD-WAN Manager | 7.5 chain | Varies | Network | 2026-04-23 |
Three Patterns from April 2026’s KEV Additions
Network infrastructure is the primary target. Three of the top five CVEs directly target network management infrastructure – FortiClient EMS, Cisco SD-WAN Manager, and Windows IKE. Compromising the device that manages your network gives attackers everything. Not one site. All of them.
The patch gap is the real vulnerability. CVE-2025-32975 had a fix available 11 months before active exploitation began. The vulnerability wasn’t the problem in March 2026 – the unpatched deployment was. Patch management isn’t optional.
Chained attacks are the standard playbook. The Cisco SD-WAN triple isn’t three separate incidents. It’s a coordinated kill chain. Modern threat actors don’t need a single 10.0-score flaw when three medium-severity CVEs chain to the same outcome. Treating each vulnerability in isolation misses the real risk.
How to Build a CISA KEV Response Workflow
Network engineers and security teams can’t manually monitor every CVE feed. Here’s a practical workflow to stay ahead of new CISA KEV additions.
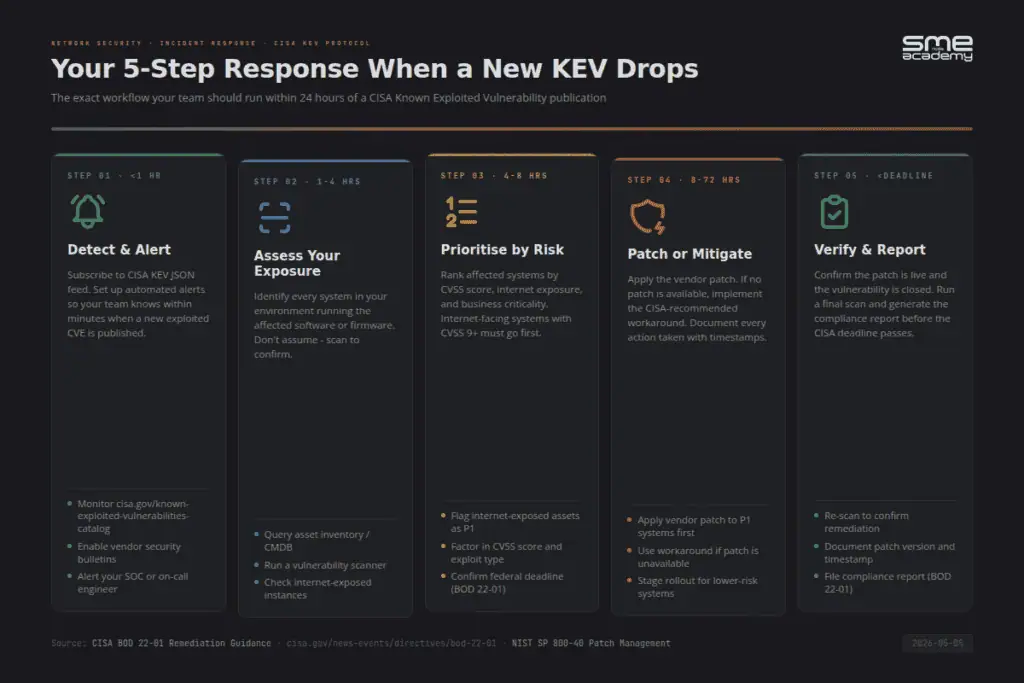
Step 1: Ingest the KEV feed directly.
CISA publishes a machine-readable JSON feed at cisa.gov/sites/default/files/feeds/known_exploited_vulnerabilities.json. Most SIEM platforms – Splunk, Microsoft Sentinel, and Wazuh – have built-in KEV integrations. When a new CVE matches your asset inventory, you should know within minutes.
Step 2: Map every KEV entry to your asset inventory automatically.
If a new KEV entry hits and you have to manually check whether you run the affected software, you’re already behind. Your CMDB should produce that answer automatically.
Step 3: Use the federal deadline as your internal SLA.
FCEB agencies get 14-21 days maximum. Use the same standard internally. If it’s good enough for U.S. federal infrastructure, it’s a reasonable private-sector baseline.
Step 4: Treat every KEV patch as a change ticket with an owner.
No KEV entry should sit in a backlog without an assigned owner and a due date.
Step 5: Report KEV patch coverage in security reviews.
CISA KEV is increasingly used as a benchmark in board-level security reporting. Your KEV remediation rate gives you a defensible, externally validated metric that means something to executives and auditors alike.
If you want hands-on training in building these detection and response workflows, our Security Operations courses cover SIEM configuration, vulnerability management, and incident response aligned to real-world threat intelligence like CISA KEV.
For structured lab exercises covering Cisco and Fortinet security configuration, the SMEnode Labs certification workbooks are worth pairing with your classroom training.
Frequently Asked Questions
What is the CISA KEV catalog?
The CISA Known Exploited Vulnerabilities catalog is a continuously updated list maintained by the U.S. Cybersecurity and Infrastructure Security Agency. It contains CVEs that meet three criteria: they have an assigned CVE ID, they have available remediation guidance, and CISA has reliable evidence of active exploitation in the wild. A KEV listing is the clearest signal available that a vulnerability is being actively weaponised – not just theoretically exploitable. As of 2026, the catalog contains over 1,200 entries.
Does CISA KEV apply to private companies?
CISA KEV’s formal requirements apply only to U.S. Federal Civilian Executive Branch agencies under BOD 22-01. Private sector organisations aren’t legally required to follow KEV deadlines. That said, a KEV listing means real attackers are targeting real organisations with this vulnerability right now. The most defensible private-sector position is to treat KEV deadlines as the benchmark for your highest-priority patch queue.
How often does CISA add new CVEs to the KEV catalog?
CISA adds new entries multiple times per month, typically in batches following major patch cycles or when new active exploitation is confirmed. In April 2026, CISA made at least five separate addition events, adding approximately 20 CVEs total. The pace has been accelerating throughout 2025-2026 as threat actors move faster from discovery to exploitation.
What was the highest CVSS score in April 2026’s CISA KEV additions?
CVE-2025-32975 in Quest KACE Systems Management Appliance received a perfect CVSS 10.0. It allows unauthenticated attackers to bypass authentication entirely through an SSO flaw, and was being actively exploited 11 months after a patch was made available.
How do I get notified when CISA adds new KEV entries?
The KEV catalog JSON feed at cisa.gov/sites/default/files/feeds/known_exploited_vulnerabilities.json can be ingested into any SIEM or ticketing system. CISA also provides email alerts at cisa.gov and posts announcements via @CISAGov. Wazuh, Splunk, and Microsoft Sentinel all have native CISA KEV integrations available.
What should network engineers do immediately after a Cisco device gets a KEV listing?
Check Cisco’s security advisory portal at sec.cloudapps.cisco.com straight away. Pull the full list of affected software versions and cross-reference your device inventory. Apply the patch within the recommended timeline – not “when the next maintenance window comes around.” Audit device logs for indicators of compromise going back at least 30 days from the KEV listing date, since exploitation typically predates public disclosure by weeks or months.
What to Do This Week
When a CVE enters the CISA KEV catalog, the question isn’t “should we patch this?” – it’s “why haven’t we patched this already?”
Check your patch status for all five CVEs in this article:
- CVE-2026-21643 – Fortinet FortiClient EMS: upgrade to 7.4.5
- CVE-2026-33824 – Windows IKE: apply April 2026 Patch Tuesday
- CVE-2025-32975 – Quest KACE SMA: apply the May 2025 patch (yes, it’s been out since then)
- CVE-2026-20133/28/22 – Cisco SD-WAN Manager: apply all three patches from Cisco’s advisory portal
- CVE-2026-34621 – Adobe Acrobat: update to v26.001.21411 or v24.001.30362
If any of these are unpatched in your environment, that’s your priority today.
Build the expertise to catch vulnerabilities like these before they become incidents. Our CCIE Security programme is taught live by instructors with real-world infrastructure experience – not pre-recorded slide decks. Explore what’s available at SMEnode Academy.